Software developed to disguise 3D printing files shared online
London designer Matthew Plummer-Fernandez has developed a piece of software that allows users to visually corrupt 3D-print files so they can't be recognised on file-sharing sites.

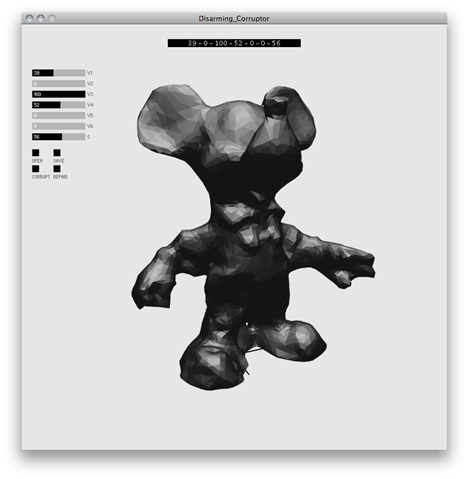
Matthew Plummer-Fernandez's Disarming Corruptor algorithm can be used to transform and disguise STL (STereoLithography) files - which record the outer shape of an object to be printed - in a way that can be only reversed by trusted recipients with the relevant key.

"Thingiverse lets you share 3D files - these get rendered, tagged, and exposed to the whole internet, and you don’t know who might be looking at them in the near future," Plummer-Fernandez told Dezeen. "Patent trolls frighten me, and so do mysterious law enforcement agencies and their web-crawling technologies."
"In a time of prolific online espionage, crackdowns on file-sharing, and a growing concern for the 3D-printing of illegal items and copyright-protected artefacts, Disarming Corruptor is a free software application that helps people to circumvent these issues," he said, adding that the project was inspired by devices such as the Enigma Machine used to encrypt and decode messages during the Second World War.
"People could alternatively just email each other encrypted files if necessary, but I wanted to devise a system where people could utilise the benefits of a sharing site and maintain a level of privacy and personal control."

After downloading Disarming Corruptor, users open the file they want to distort then use slide bars to set seven values that are displayed as an encryption key at the top of the screen.
Pressing Corrupt transforms the shape according to these settings and saves the new file plus an image of the encryption key in the same location as the original. The disguised object can then be uploaded to a public file-sharing site like Thingiverse and the decoding key distributed to a few trusted people.
The last slider controls how much the form is corrupted, so the result can retain some recognisable elements. "This could be useful for instances where you might want simply make functional object inoperative until keys are shared," the designer suggests.

To restore the file to its original form, the recipient needs both the application and the unique seven-digit settings used by the sender. They simply open the corrupted version in the Disarming Corruptor program, move the sliders to generate the correct key in the top bar and click Repair. Entering the incorrect settings to decode the file would just damage it further.

"I know there are a lot of harmless copyright infringements already on Thingiverse," Plummer-Fernandez continued. "Think of all the Yoda Heads out there. These are exposed to all the patent and copyright trolls to dive in and pick out victims, and I'm sure the small print on these sharing services leaves their communities hanging out to dry when they come for them."
"When patent trolls and law enforcement agencies find these files on sharing sites they will only see abstract contortions, but within the trusting community these files will still represent the objects they are looking for, purposely in need of repair," he said.
The software is free and available for Mac OSX, and Plummer-Fernandez is working on exports for Linux and Windows.
Plummer-Fernandez was born in Colombia and now lives in London, where he graduated from the Royal College of Art's Design Products MA in 2009, and creates his own 3D-editing tools for design projects like the 3D-printed vessels made by scanning and manipulating everyday objects that he presented this time last year.